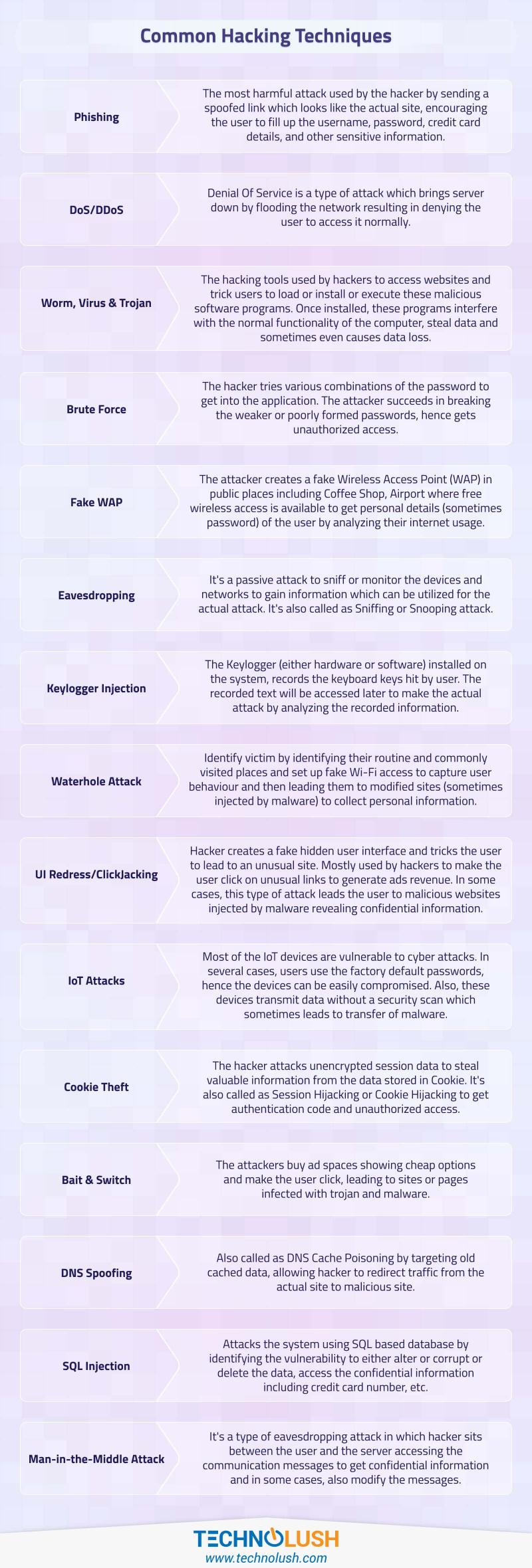
This post provides the list of commonly used hacking techniques used by hackers to exploit internet users. It's not an exhaustive list and covers only the most common attacks.
Phishing
The most harmful attack used by the hacker by sending a spoofed link which looks like the actual site, encouraging the user to fill up the username, password, credit card details, and other sensitive information. The spoofed links look almost the same as the original brand, hence several users fall in the trap and provide the confidential details.
DoS/DDoS
Denial Of Service is a type of attack which brings the server down by flooding the network resulting in denying the user to access it normally. The attacker uses several systems targeting the server by sending multiple requests at a much larger rate resulting in the unavailability of the server to regular users. Sometimes it also leads to a server shut down by completely blocking the server.
Worm, Virus & Trojan
The hacking tools used by hackers to access websites and trick users to load or install or execute these malicious software programs. Once installed, these programs interfere with the normal functionality of the computer, steal data and sometimes even causes data loss. The worms are more harmful as compared to viruses since these are self-replicating or self-propagating causing more damage.
Brute Force
The hacker tries various combinations of the password to get into the application. The attacker succeeds in breaking the weaker or poorly formed passwords, hence gets unauthorized access. The user can make it hard for attackers by providing strong password having a combination of alphabetical characters, numbers and special characters.
The service providers must also take important measures to limit the rate at which users can try to login to the system, resulting in low combinations over a period of time.
Fake WAP
The attacker creates a fake Wireless Access Point (WAP) in public places including Coffee Shop, Airport where free wireless access is available to get personal details (sometimes password) of the user by analyzing their internet usage. The fake Wireless Access Point mimic the real name, hence making users connect to the wireless network.
Eavesdropping
It's a passive attack to sniff or monitor the devices and networks to gain information which can be utilized for the actual attack. It's also called as Sniffing or Snooping attack. The attacker monitors the network traffic to capture the relevant details. All the online services which involve user accounts must use SSL provided by safer Certificate Authority (CA) by default to avoid such attacks.
Keylogger Injection
The Keylogger installed on the system records the keyboard keys hit by the user. The recorded text will be accessed later to make the actual attack by analyzing the recorded information. The Keylogger can be either hardware or software. It can also trigger emails having the recorded keys.
Waterhole Attack
The attacker closely monitors user activities and target a group of users in this type of attack. It involves identifying the victim by analyzing their routine and commonly visited places and set up fake Wi-Fi access to capture user behavior and then leading them to modified sites (sometimes injected by malware) to collect personal information.
UI Redress/ClickJacking
Hacker creates a fake hidden user interface and tricks the user to lead to an unusual site. Mostly used by hackers to make the user click on unusual links to generate ads revenue. In some cases, this type of attack leads the user to malicious websites injected by malware revealing confidential information. It can be avoided by properly securing web servers and websites.
IoT Attacks
Most of the IoT devices are vulnerable to cyber attacks. In several cases, users use the factory default passwords, hence the devices can be easily compromised. Also, these devices transmit data without a security scan which sometimes leads to the transfer of malware.
The device owner must set a secure password and share with authentic users where applicable in order to reduce these type of attacks.
Cookie Theft
The hacker attacks unencrypted session data to steal valuable information from the data stored in Cookie. It's also called as Session Hijacking or Cookie Hijacking to get authentication code and unauthorized access. The session data must also be secured apart from using SSL.
The website must send cookies with the HttpOnly flag set to avoid modification on the client side using JavaScript.
Bait & Switch
The attackers buy ad spaces showing cheap options and make the user click, leading to sites or pages infected with trojan and malware.
DNS Spoofing
Also called DNS Cache Poisoning by targetting old cached data, allowing a hacker to redirect traffic from the actual site to malicious site.
SQL Injection
Attacks the system using SQL based database by identifying the vulnerability to either alter or corrupt or delete the data, access the confidential information including credit card number, etc.
Man-in-the-middle Attack
It's a type of eavesdropping attack in which hacker sits between the user and the server accessing the communication messages to get confidential information and in some cases, also modify the messages.